Managing access across your organization means your IT team constantly updates permissions, creates accounts, and revokes access manually. Identity-driven workflows connect your identity system to your service desk, so these changes happen automatically when someone's role or employment status changes. We break down which integrations reduce manual work instead of just checking a compliance box.
TLDR:
Identity provider integrations automate user provisioning and access control in ITSM tools.
SAML, OIDC, and SCIM protocols sync employee data and trigger automated workflows.
SSO reduces password reset tickets while maintaining security through centralized control.
Most integrations only handle authentication without automating downstream ticket actions.
Ravenna functions as an agentic workflow automation platform that orchestrates identity-driven workflows across tools like Okta and Google Workspace, executing tasks directly within Slack without manual intervention.
What Are Identity Provider Integrations for ITSM?
Identity provider integrations connect authentication systems like Okta, Microsoft Entra ID, or Auth0 directly with IT service management tools as part of a broader identity and access management strategy. These integrations verify user identities, grant appropriate access levels, and sync employee data across systems automatically. During onboarding and offboarding, or when someone changes roles, identity provider integrations keep your service desk synchronized. They close the gap between who has access and who should have access based on current employment status and role.
The value comes from automation. Instead of IT agents manually resetting passwords, provisioning accounts, or updating permissions, these integrations enable automation by providing authoritative identity data. Single sign-on (SSO) lets employees access your ITSM system with one set of credentials while the identity provider handles authentication in the background.
For security teams, this creates centralized control over access policies. You can enforce multi-factor authentication (MFA), automatically revoke access when employees leave, and maintain audit trails of who accessed what and when. For IT support teams, it reduces routine tickets and frees up time for complex issues that need human attention.
How We Ranked Identity Provider Integrations for ITSM
We assessed identity provider integrations and other IAM tools based on how well they reduce manual IT work and improve access management for service desk teams:
Protocol support is critical. The strongest integrations implement SAML 2.0, OpenID Connect (OIDC), and SCIM for automated user provisioning. SCIM syncs employee data in real time instead of requiring manual updates.
Automation depth separates basic integrations from advanced ones. The best solutions automatically provision accounts, handle deprovisioning when users leave, and update permissions using role-based access control (RBAC) policies. They also trigger ITSM workflows directly from identity events, creating tickets or executing access requests without human input.
SSO implementation quality matters. Integrations that require minimal configuration and provide clear documentation perform better. Users should authenticate once and access all connected systems.
Finally, we looked at compatibility with popular ITSM tools and whether each provider supports identity-driven ticket resolution, where access requests get automatically approved or denied based on predefined policies.
Best Overall Identity Provider Integration for ITSM: Ravenna
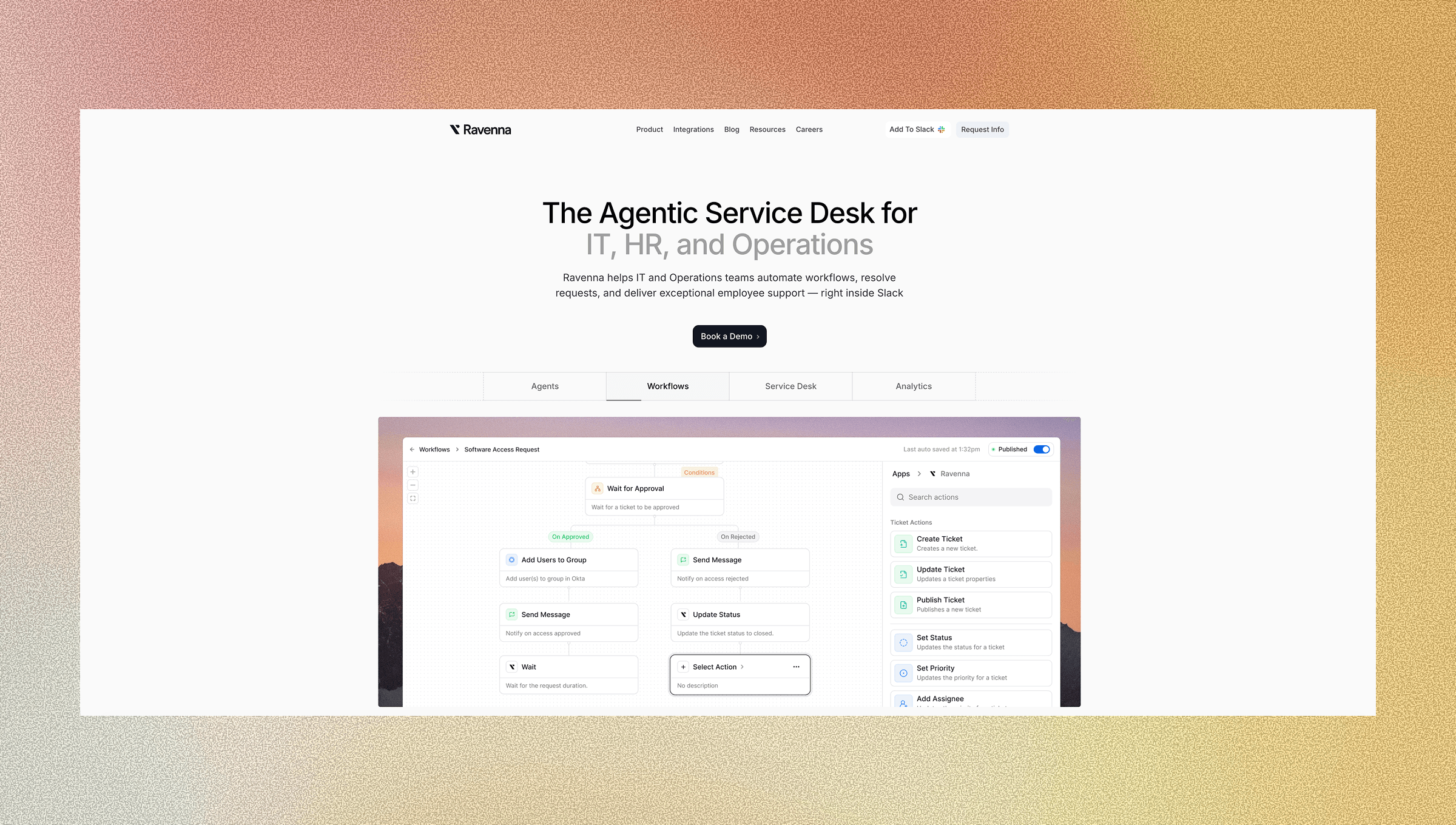
Ravenna operates as an agentic workflow automation platform that automates end-to-end workflows across IT, HR, and Operations teams. Connecting Okta, Microsoft Entra ID, and Google Workspace directly to Slack allows specialized agents, such as the IT Agent or PeopleOps Agent, to execute complex tasks without human intervention.
The platform’s automation engine moves beyond simple answers to perform actual work. When an employee requests a password reset or software license, Ravenna validates their identity against your IdP and executes the necessary actions in the background. A visual workflow builder allows teams to construct logic-based routing, so that provisioning events or role changes automatically update access rights.
Managers approve requests in Slack with full context from the identity hierarchy, while the system handles the manual execution. This approach removes the need for separate portals and keeps the entire service desk experience within the communication tool employees already use.
Okta
Okta provides enterprise-grade identity and access management with extensive ITSM integration capabilities through its Integration Network. The company specializes in centralized authentication across hundreds of applications, including most major service desk tools.
Key Features
Okta includes a number of key features for identity provider integration:
SAML and OIDC SSO for ITSM authentication
SCIM-based user provisioning to service desk tools
Pre-built connectors for ServiceNow, BMC Remedy, and other ITSM solutions
Lifecycle management hooks for ticketing workflows
Limitations
Okta requires separate integrations for each ITSM tool and does not provide native AI-powered ticket resolution or conversational workflows.
Organizations must manually configure user provisioning rules and ticket routing logic through workflow policies and API configurations.
Okta is good for large enterprises with complex identity governance requirements and existing Okta deployments seeking to extend SSO to their ITSM tools.
Microsoft Entra ID
Microsoft Entra ID (formerly Azure Active Directory) offers cloud-based identity and access management with growing ITSM integration support through standard protocols.
Key Features
Microsoft Entra ID includes a number of key features for identity provider integration:
Azure AD SSO for ITSM portal authentication with conditional access policies controlling service desk access.
User and group synchronization to ITSM systems with Microsoft 365 ecosystem integration for authentication workflows.
App registrations for manual ITSM configuration, though custom automation tools are required for identity-driven ticket workflows.
Limitations
Entra ID integration with ITSM requires manual configuration and does not include automated identity-driven ticket workflows or AI resolution capabilities.
IT teams must build custom automation between identity events and service desk actions using external tools.
Microsoft Entra ID is good for organizations invested in Microsoft 365 that need SSO and user provisioning for their ITSM tools.
OneLogin
OneLogin provides cloud-based identity management with SSO capabilities for ITSM applications.
Key Features
OneLogin includes a number of key features for identity provider integration:
Pre-configured ITSM app connectors supporting major service desk tools
SAML 2.0 and OIDC authentication protocols for secure access
Basic user provisioning through SCIM standards
Multi-factor authentication options for service desk access
Limitations
OneLogin's ITSM integrations focus primarily on authentication and lack native support for identity-driven automation workflows.
Organizations cannot automatically trigger ticket creation, access approvals, or provisioning tasks based on identity events without custom development.
OneLogin is good for mid-market companies seeking straightforward SSO implementation for their ITSM portals without extensive customization requirements.
Auth0
Auth0 delivers developer-friendly identity management with flexible authentication options for ITSM applications.
Key Features
Auth0 includes a number of key features for identity provider integration:
Customizable authentication flows via Rules and Actions
Multiple protocol support (SAML, OIDC, OAuth)
API-first architecture for ITSM integration
Extensible identity pipeline
Limitations
Auth0 requires developer resources to implement ITSM integrations and does not offer pre-built workflows for common service desk scenarios like automated access provisioning, password reset automation, or identity-triggered ticket routing without custom code.
Auth0 is good for development teams that need granular control over authentication logic and have resources to build custom ITSM identity integrations.
Feature Comparison Table of Identity Provider Integrations
Feature | Ravenna | Okta | Microsoft Entra ID | OneLogin | Auth0 |
SSO Protocol Support | SAML, OIDC | SAML, OIDC | SAML, OIDC | SAML, OIDC | SAML, OIDC, OAuth |
ITSM Tool Compatibility | ServiceNow, BMC Remedy, and other ITSM tools via workflow integrations | Requires manual configuration | Pre-configured connectors | API-based custom integration | |
Automated User Provisioning | Yes (real-time sync) | Yes (SCIM) | Yes (manual setup) | Yes (SCIM) | Requires custom development |
Identity-Driven Workflow Automation | Yes | Manual configuration required | Requires external tools | No | Requires custom code |
AI-Powered Ticket Resolution | Yes | No | No | No | No |
Conversational Interface | Slack-native | No | No | No | No |
Setup Complexity | Low | High | Medium | Medium | High (developer-required) |
Native Slack Integration | Yes | No | No | No | No |
Why Ravenna Is the Best Identity Provider Integration for ITSM
Most identity provider integrations stop at authentication. They verify who you are, sync your user record, and stop there. Identity systems work best when they trigger downstream actions, such as access reviews and policy updates, not simply gate access.
Ravenna uses identity data as the foundation for automated workflows. When your identity provider updates an employee's role or department, we immediately adjust ticket routing, approval chains, and access permissions. Your service desk stays synchronized with organizational changes without manual updates. This automation layer augments IT teams rather than replacing them, freeing support staff from routine identity management tasks so they can focus on complex issues that require human expertise and judgment.
The Slack-native design eliminates the friction that breaks most IdP integrations. Employees request access where they already work, and approvers see full context from your identity hierarchy without switching tools.
While SAML and OIDC protocols handle authentication, Ravenna extends that foundation into actual workflow execution. Its specialized agents process access requests using identity attributes, organizational policies, and historical patterns to auto-approve routine requests or route complex ones to the right person.
Final Thoughts on Selecting Identity Provider Integrations for ITSM
Authentication is just the starting point for identity provider integrations. Your service desk needs automated provisioning, role-based ticket routing, and access request resolution without manual intervention. Most identity providers handle SSO well, but connecting identity events to service desk actions is where you save time and streamline service desk operations. Choose integrations that work with your existing tools and reduce the number of systems your team needs to check.
To see how Ravenna can automate your workflows, schedule a demo.
FAQ
Which identity provider integration works best for teams already using Slack?
Ravenna is built for Slack-based workflows, letting employees request access and managers approve directly in Slack using identity data from Okta, Microsoft Entra ID, or Google Workspace. Other providers like Okta and Auth0 require separate portals and custom development to connect identity events with service desk actions.
How do I choose between Okta and Microsoft Entra ID for ITSM integration?
Choose Okta if you need pre-built connectors for ServiceNow or BMC Remedy and have complex identity governance requirements across multiple applications. Pick Microsoft Entra ID if your organization already uses Microsoft 365 and wants to extend that authentication to your service desk with minimal additional licensing costs.
Can identity provider integrations automatically resolve access requests without IT involvement?
Yes, but implementation varies by provider. Ravenna uses specialized agents to auto-approve and execute routine access requests based on identity attributes, while Okta and OneLogin require manual configuration of provisioning rules and cannot trigger automated ticket resolution without custom development work.
What's the difference between SSO and automated user provisioning in ITSM integrations?
SSO handles authentication by verifying user identity when they log into your service desk, while automated user provisioning syncs employee data (roles, departments, permissions) between your identity provider and ITSM tool in real time. Most providers support SSO through SAML or OIDC, but only some offer true automated provisioning via SCIM protocols.
When should I consider an identity provider integration that includes AI-powered workflows?
If your IT team handles high volumes of repetitive access requests, password resets, or permission changes that follow predictable patterns based on employee roles and departments. Agentic platforms like Ravenna can execute these workflows automatically, while traditional providers require manual ticket handling or extensive custom automation development.




